The perimeter of any site is the ideal place for a security implementation to start. It represents the first point of intrusion into a private area, and enables detection of intruders at the earliest time, which creates a greater time-window for threats to be nullified. Despite this, emphasis on detection at the perimeter remains low in many applications, despite increasingly efficient technologies being available to counter any threats.
The perimeter represents a very important element in any security plan. It is often the first point at which a demarcation between public and private land is made, and represents the earliest opportunity for a site to define when a target – whether welcome or not – has entered its space.
Whether a perimeter is designed to prevent ingress or simply to identify that the status of the area has changed, it is important to be aware of the need to have an identifiable and obvious boundary. Whether this is a six foot fence festooned with razor wire or a simple low height wall which can be stepped over will be dependent upon the needs of each individual site. What is more important is that anyone entering a private area is aware they have done so.
By creating an obvious barrier, it can then be considered persons within the protected area have made a conscious decision to be there. However, it makes sense to also consider whether a perimeter can be adapted to enhance the security of the location.
For many, the term ‘perimeter protection’ summons up images of physical barriers. There is nothing wrong with a physical approach to perimeter protection, but such elements will not offer complete protection. One consideration when selecting a physical security solution is that these products work by making it too difficult or time-consuming for criminals to gain entry. The hope is that they’ll be deterred or give up and move on a softer target.
 To be more effective, physical measures need to be used in conjunction with other systems. For example, a high fence will be scaled by a determined criminal, leaving the site vulnerable unless the intrusion is reported by a monitoring system.
To be more effective, physical measures need to be used in conjunction with other systems. For example, a high fence will be scaled by a determined criminal, leaving the site vulnerable unless the intrusion is reported by a monitoring system.
Given the depth of options with regard to technology-based perimeter detection devices, it makes sense to implement these, either as part of a layered approach or linked with other systems to create a more holistic approach to site security.
Adding systems
Electronic perimeter security systems such as buried systems or fence-mounted solutions are often the exclusive preserve of high-risk large and open sites. Lower risk applications tend to select physical options. However, the evolution of various sensor technologies, coupled with increased economies of scale, have resulted in the reduction of equipment costs. Additionally, enhancements to sensor technology has made the use of external detectors a realistic option for all applications.
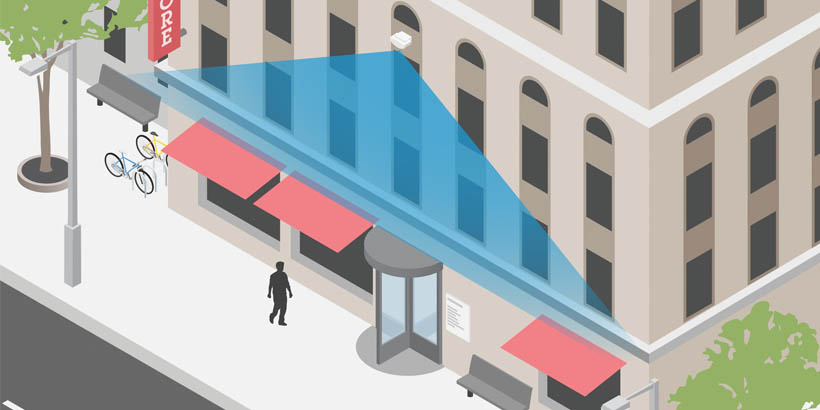
While the installation of physical measures does appeal to users, such elements are not exactly proactive, but this isn’t to say physical elements at the perimeter do not have a role to play when looking at technology-based options. They can act to create a sterile zone – an area where the boundary is established, and beyond which any intrusion can be deemed to be an event that requires some form of action.
Sterile zones are a common in many detector-based electronic perimeter solutions, because they simplify the generation of exceptions. If a sterile zone exists and all activity within it is prohibited, then any exceptions are clearly violations. This subsequently enhances the use of sensors, because the solution starts with a simple premise that nothing should occur in the sterile zone.
It’s worth considering the users’ goals when establishing which technologies to deploy in an electronic perimeter system. In truth, this is usually a simple task. Most end users want to be informed of an intrusion as quickly as possible. This is a key consideration in perimeter protection design. Rather than delay intruders with obstacles that can be defeated in time, or capture video footage to be reviewed after the event, end users would rather take action and manage any intrusion as swiftly as possible.
Proactive design
The use of detection technologies to create an early warning of intrusion is well established, but in the past security industry standards relating to police response shifted the emphasis onto internal detection. This was because of the increased stability such an approach offers.
 Due to budgetary constraints and a lack of resources, police response to alarms has become somewhat hit and miss. The number of high profile cases where police simply do not respond, or where policies prevent a timely intervention, have made it increasingly important for many end users to achieve the earliest warning possible. The most efficient and cost-effective way to achieve this is via the use of sensors at the perimeter.
Due to budgetary constraints and a lack of resources, police response to alarms has become somewhat hit and miss. The number of high profile cases where police simply do not respond, or where policies prevent a timely intervention, have made it increasingly important for many end users to achieve the earliest warning possible. The most efficient and cost-effective way to achieve this is via the use of sensors at the perimeter.
Perimeter protection can require solutions which deliver longer range detection, especially when applications have large open areas. There are a variety of options. Often the choice will come down to what the site requirements are and the physical characteristics of the protected area.
Choices can include passive infrared detectors, active infrared detectors, radar and LiDAR sensors, microwave detectors and multi-technology units. Many manufacturers offer wireless versions of external detectors, and these can simplify installation where cabling to a perimeter might be costly.
Passive detectors monitor large open areas and detect motion anywhere in their field of view. These devices predominantly makes use of infrared sensing. There are also a number of multi-technology units, combing – for example – passive infrared and microwave sensing – which offer a variety of coverage patterns and ranges. While these devices use advanced signal processing to filter out sources of nuisance alarms, there will inevitably be a degree of risk to stability in some external locations.
Increasingly, sites are using passive detection devices in double-knock configurations. This involves linking the detection device with other detectors or video cameras. This ensures that if an event occurs, it is only signalled as an alarm if both elements simultaneously trigger.
External passive detection devices offer a cost-effective solution. There are many passive detection options with very clever dual sensor designs, but these are predominantly aimed at shorter detection distances, although some can be used over extended ranges.
 Photoelectric beams are active detection devices, and enhance the level of reliability on offer thanks to ongoing research and development by the leading manufacturers. These work by protecting a straight line between points, usually following a perimeter. Unlike space detection devices, they don’t cover open areas.
Photoelectric beams are active detection devices, and enhance the level of reliability on offer thanks to ongoing research and development by the leading manufacturers. These work by protecting a straight line between points, usually following a perimeter. Unlike space detection devices, they don’t cover open areas.
Over the years the operation of photoelectric beams has been enhanced, with significant advances in terms of processing and stability. The days of wind-borne rubbish or small animals and birds triggering the units are over, and tamper and sabotage attempts have also been largely eliminated.
As with passive detectors, ranges do tend to vary, with distances into the hundreds of metres being achievable. There are two approaches to active beam-based detection. Systems can either make use of transmitter and receiver units, one at each end of the link, or a single transceiver can be used with a reflector.
As is the case with passive detectors, infrared beam units can be linked with other technologies, or indeed with other detection devices, to create a double knock scenario. For example, a site with infrared beams at the perimeter could link these with space detection covering open areas. Alternatively, the beams could be linked with analytics using either video or thermography for a more complete solution.
READ MORE ABOUT ACTIVE INFRARED DETECTORS AND THE AVAILABLE OPTIONS
 Laser-based detection devices are another option, and the choice of available devices is growing. One benefit of laser-based sensors is that there are units which can deliver exact positioning information.
Laser-based detection devices are another option, and the choice of available devices is growing. One benefit of laser-based sensors is that there are units which can deliver exact positioning information.
While many detectors identify the area which is in alarm via zoning, laser sensors can pinpoint targets using X-Y coordinates. With appropriate software, this information can be used to track targets around a site, adding to the useful data supplied in the case of an early warning system.
Fence-mounted systems are another technology which has not only developed to offer greater levels of performance, but have also become more affordable thanks to on-going advances. Economies of scale have also ensured that prices are competitive, making such solutions ideal for a wider range of applications.
In summary
In recent years the technology used for perimeter protection has evolved, making the delivery of such systems more cost-effective. Because of this, an increasing number of sites could benefit, including those with small grounds or limited surrounding areas.
The various technologies have become superior in terms of performance and stability. Not only do they allow perimeter protection, but they can also be used as a trigger for other systems. Despite this, too many still view electronic perimeter solutions as a high risk option. Demand for secure perimeters is growing at a rapid pace, and such thinking is out-dated!