 Multilayered security solutions are a comprehensive approach to safeguarding assets, systems, and personnel by implementing multiple layers of defence against potential threats. Instead of relying solely on one security measure, multilayered security involves integrating various technologies, protocols, products and practices to create a robust and resilient security infrastructure.
Multilayered security solutions are a comprehensive approach to safeguarding assets, systems, and personnel by implementing multiple layers of defence against potential threats. Instead of relying solely on one security measure, multilayered security involves integrating various technologies, protocols, products and practices to create a robust and resilient security infrastructure.
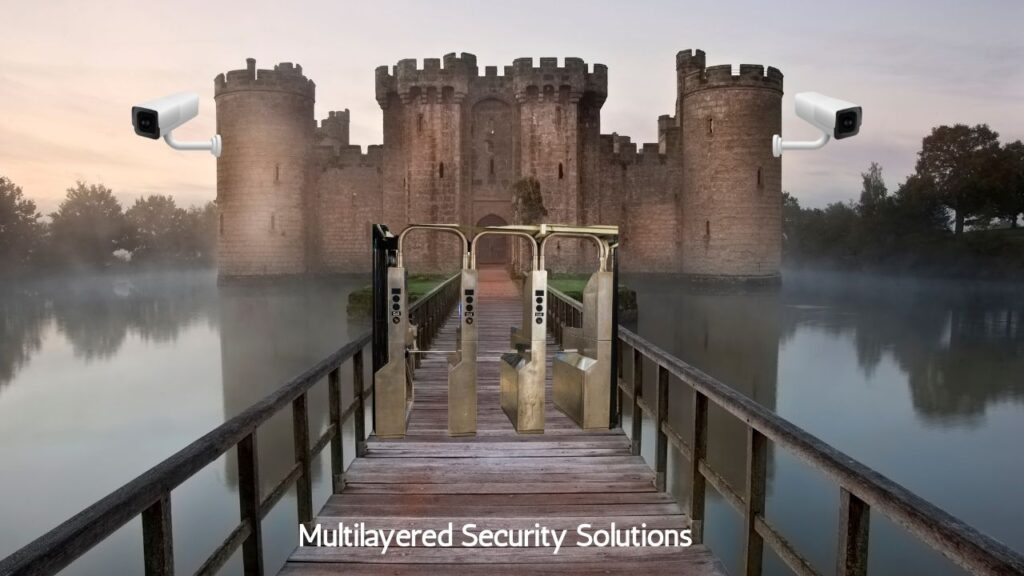
The concept of multilayered security is akin to the defence mechanisms of a castle, which typically had multiple barriers such as moats, walls, gates, and guards to protect against intruders. Similarly, multilayered security may involve combinations of physical barriers, access controls, surveillance systems, intrusion detection systems, encryption, authentication mechanisms, and cybersecurity measures in modern security contexts.
Each layer of security adds an additional barrier to prevent or mitigate different types of threats. For instance, physical barriers like fences and locks may deter unauthorised access, while access controls such as biometric authentication or keycards restrict entry to authorised personnel. Meanwhile, surveillance cameras and motion detectors provide real-time monitoring and detection of suspicious activities.
By implementing multiple layers of security, organisations can create a more resilient defence system that effectively addresses various potential vulnerabilities and mitigates risks. This approach minimises the likelihood of successful security breaches and enhances overall protection for assets, data, and personnel.
As we delve into researching innovative physical security approaches, specifically focusing on the multilayered approach for a feature article on Benchmark, Ajax Systems and i-PRO shared their expertise in providing multilayer security solutions.
In this context, i-PRO focuses on integrating AI video analytics into its cameras and collaborating with third-party solution providers.
Ajax has a broader offering includes access control, perimeter surveillance, and various detectors for flooding, fire, and other threats.
Q: What technologies and strategies does Ajax employ to monitor and control access?
Ajax: The Ajax system leverages a combination of robust communication, intrusion, fire, and flood detectors for ultimate outdoor and indoor security, as well as advanced video surveillance.
The system utilises innovative proprietary technologies like Jeweller, Wings, and JetSparrow, ensuring fast and reliable device communication. Motion detectors are equipped with intelligent algorithms to detect and distinguish between human movements and false alarms accurately, ensuring high precision. Openings, fire, and flood detectors are strategically placed to provide comprehensive coverage. At the same time, video surveillance solutions incorporate high-resolution cameras and cloud-based storage for real-time monitoring and seamless access to footage.
Additionally, Ajax places a strong emphasis on user-friendly control and monitoring. Through dedicated mobile apps, users can effortlessly manage and monitor their security system remotely, receiving instant notifications and alerts when any suspicious activity is detected.
Ajax’s cloud-based management platform enables centralised control of access points and security devices. This centralised approach simplifies administration, monitoring, and maintenance across multiple layers of security, ensuring a streamlined and efficient management process.
Q: How is video analytics integrated into surveillance solutions?
i-PRO: i-PRO integrates AI video analytics into over 200 products as a default. It offers unmatched innovation and data-driven decision-making across a variety of scenarios. i-PRO ensures accurate data analysis, real-time alarms and cost-effective surveillance using the Ambarella processors for solutions at the edge.
The growth of the CCTV industry has been exponential, generating vast amounts of video data that are impossible to manage manually, requiring advanced analytics. Edge analytics, a subset of AI, enables real-time data analysis at the source, reducing latency and facilitating rapid decision-making, crucial for swift responses to security threats.
In a recent case study, i-PRO implemented multi-sensor cameras for the Italian police in Val Trompia, using edge-AI capabilities for motion detection, people and vehicle counting, plus a proactive watchlist. This innovative solution not only led to an 80% reduction in criminal activity in a local park. Moreover, it ensured the local community’s protection whilst leveraging privacy-focused AI.
i-PRO’s commitment to innovative hardware is evident in the launch of the X series range, which transforms non-AI cameras into smart devices, making them even smarter through on-site learning applications. In this way, the X series facilitates AI adoption, reduces installation costs, accelerates data analysis, and ensures compatibility with evolving needs.
Ajax: Harnessing the power of the proprietary JetSparrow technology, Ajax cameras blend high-definition surveillance with unparalleled privacy safeguards. Designed for versatility, they’re apt for both indoor and outdoor environments with their IP65 rating. The passwordless authentication ensures a seamless and secure setup. With various matrix types and lenses, cameras accommodate various surveillance needs.
Also, using AI-analysis capabilities, Ajax cameras can detect and recognise object types, such as humans, vehicles, and pets. This allows the surveillance system to record only relevant events (like a human entering the room or a car passing through the parking lot) and use less storage.
Q: Are there specific technologies or tools from Ajax designed to enhance the collaboration between technology and human resources?
Mobile Apps and User Interfaces: Ajax provides intuitive mobile apps and user interfaces, allowing users to interact with and control security systems easily. This facilitates seamless collaboration as users can receive real-time alerts, monitor security status, and control devices remotely.
Cloud-Based Management: Ajax’s cloud-based management platform enables centralised control of security devices. This facilitates efficient collaboration by allowing human resources to manage and monitor security systems from a unified platform, irrespective of geographical location.
Customisable Scenarios and Automation: Ajax’s devices for comfort and productivity include smart switches, air quality detectors, smart plugs and other automation devices. They allow controlling the power supply of the venue, or certain electrical appliances, or light via the Ajax mobile app. Thanks to automation scenarios, it’s possible to configure Ajax to automatically shut down the water to prevent flooding, cut off power by a fire alarm, schedule the work of the system or other appliances in the house, etc.
Q: How does iPro help to improve human resource collaboration and technology integration?
The use of Edge-based analytics and an open platform has enabled the integration of many Analytics from 3rd parties into the i-PRO cameras. Once Vaxtor has developed such a range of integrations, these include LPR, MMC, general purpose OCR, and container recognition.
LPR and MMC enable the cameras to detect and process the number plates of vehicles, recognise the make, models, colour and classification of vehicles and then provide this information via open protocols to backend systems. This approach enables the standard CCTV cameras to provide valuable information on the cars now on-site and provide the information to the access control system, parking system, BMS solutions and others.
General purpose OCR has enabled the detailed tracking of any object, including a human-readable visible ID. Integrating via open protocols enables the data to be captured along with the video to provide a log of where, what and when. The advantage of using the human-readable ID is that many existing processes can be quickly and easily digitised and automated while retaining manual processing ability.
Container recognition enabled the capture of the registration information of containers while they moved through the complex distribution network.
Multilayer security requires a holistic approach
For a reliable multilayered security solution, there needs to be a proactive and comprehensive approach to security. With Ajax Systems and i-PRO, we have witnessed how these industry leaders spearhead innovations to fortify security infrastructures and protect against evolving threats.
From Ajax Systems’ cutting-edge offerings in perimeter monitoring, access control, and video analytics integration to i-PRO’s revolutionary edge-AI capabilities and commitment to privacy-focused surveillance solutions, both companies exemplify the fusion of advanced technology with human-centric principles to create resilient security ecosystems.
Multilayered security enables organisations to improve their resilience, adaptability, and responsiveness to emerging threats, thereby safeguarding their assets, data, and personnel.

